IOC
Indicators of Compromise
IOC (Indicators of Compromise)
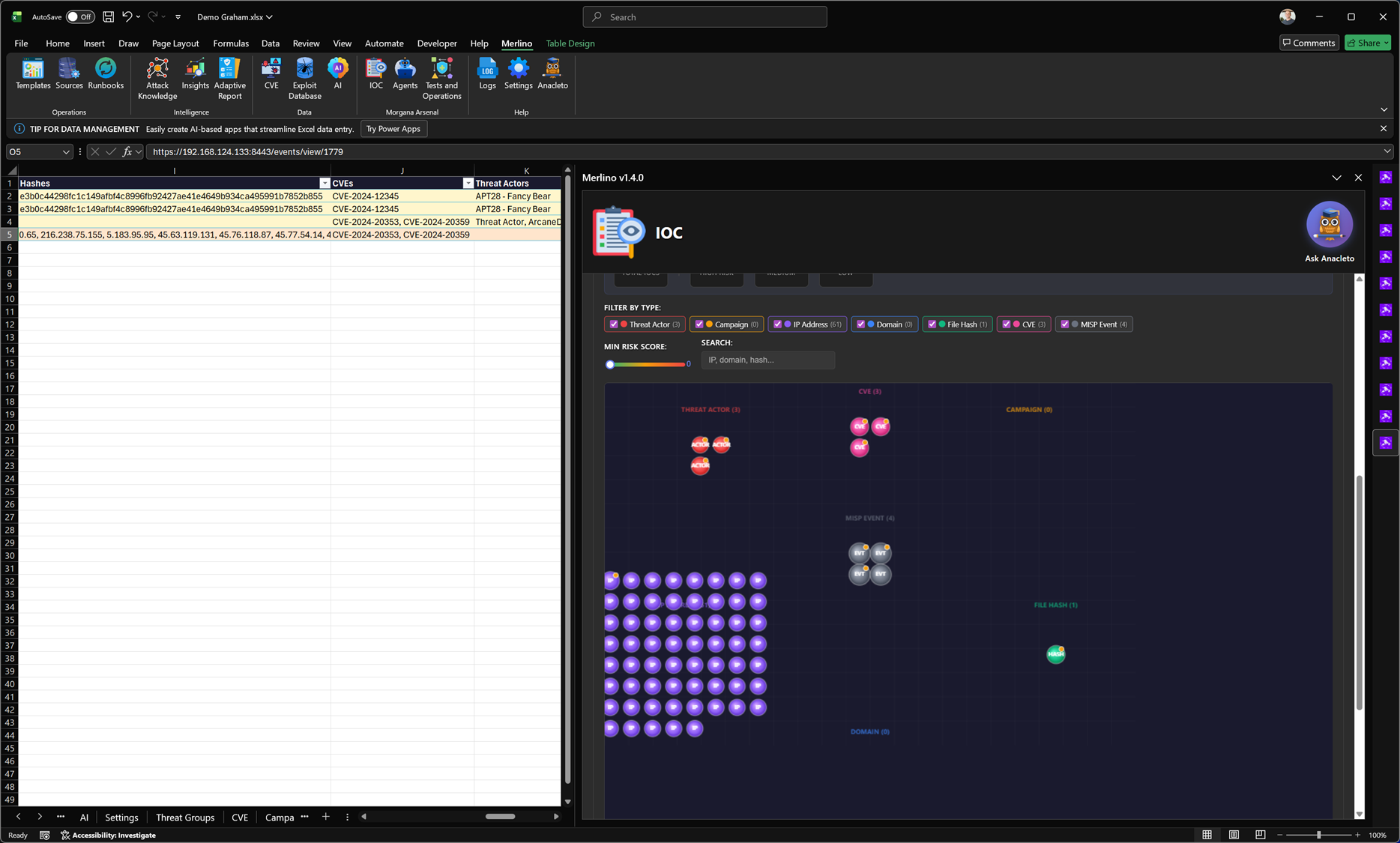
IOC is Merlino’s workspace for Indicators of Compromise and connected CTI entities. It centralizes indicators and intelligence objects in one view and provides built-in integration with MISP for sharing, enrichment, and re-ingestion of improved CTI back into the workbook.
What it is
IOC provides a unified interface to manage and explore CTI objects that typically live across multiple tools and formats. It supports day-to-day analysis (filtering, searching, and prioritizing) as well as operational workflows where indicators need to be exported, enriched, and synchronized with external CTI platforms.
What you can manage
IOC supports mixed intelligence datasets and allows you to work with multiple entity types in a single interface. Typical supported objects include:
- IP addresses and related network indicators
- Domains and URL-based indicators
- File hashes (malware artifacts and samples)
- CVEs and vulnerability-linked intelligence context
- Threat actors and attribution entities
- Campaigns and activity groupings
- MISP events and event-derived indicator collections
Filtering and exploration
IOC is designed for rapid triage. You can filter by indicator type, search across values, and apply basic scoring thresholds to focus on what matters most. The interface helps you quickly isolate subsets of indicators for investigation or export.
- Filter by type: narrow the view to specific indicator categories (IPs, domains, hashes, CVEs, actors, campaigns, events).
- Search: locate indicators by partial value (for example part of a domain, hash prefix, or CVE ID).
- Risk threshold: focus on indicators above a minimum risk score when prioritizing action.
MISP integration
Merlino is fully integrated with MISP (Malware Information Sharing Platform), a widely used open-source platform for sharing, enriching, and correlating cyber threat intelligence. MISP helps teams exchange structured CTI, apply tagging and taxonomy, build relationships between entities, and enrich indicators with additional context.
Export to MISP
IOC allows you to publish selected indicators and CTI entities to MISP as structured events. This supports collaboration and enables external enrichment workflows (tags, relationships, additional indicators, correlation with other events).
- Structured publishing: export indicators as MISP-compatible attributes/events rather than unstructured text.
- Event building: group indicators into meaningful events aligned to campaigns, actors, or investigations.
- Sharing-ready: prepare CTI for collaboration across teams or partners using MISP’s sharing controls.
Re-import enriched intelligence
After enrichment in MISP, IOC can re-import the improved intelligence back into Merlino. This keeps the workbook aligned with the latest CTI context and ensures that enrichment is not lost in a separate platform.
- Enriched context: pull back tags, relationships, and expanded indicator sets.
- Continuous improvement: maintain an iterative cycle of export → enrich → re-ingest.
- Operational reuse: use enriched intelligence in other Merlino modules (mapping, reporting, validation workflows).
Why it matters
IOC reduces fragmentation in CTI handling. It gives you a practical way to keep intelligence actionable inside Merlino while still leveraging MISP as a dedicated CTI sharing and enrichment platform. The result is faster triage, richer context, and a consistent intelligence base that can feed analysis, detection mapping, and validation activities.
Note: MISP integration enables a bidirectional workflow. Merlino does not replace MISP; it connects to it so CTI can be operationally used, enriched externally, and synchronized back as part of a repeatable intelligence lifecycle.
