Sources
Sources (Data Import & Intelligence Enrichment)
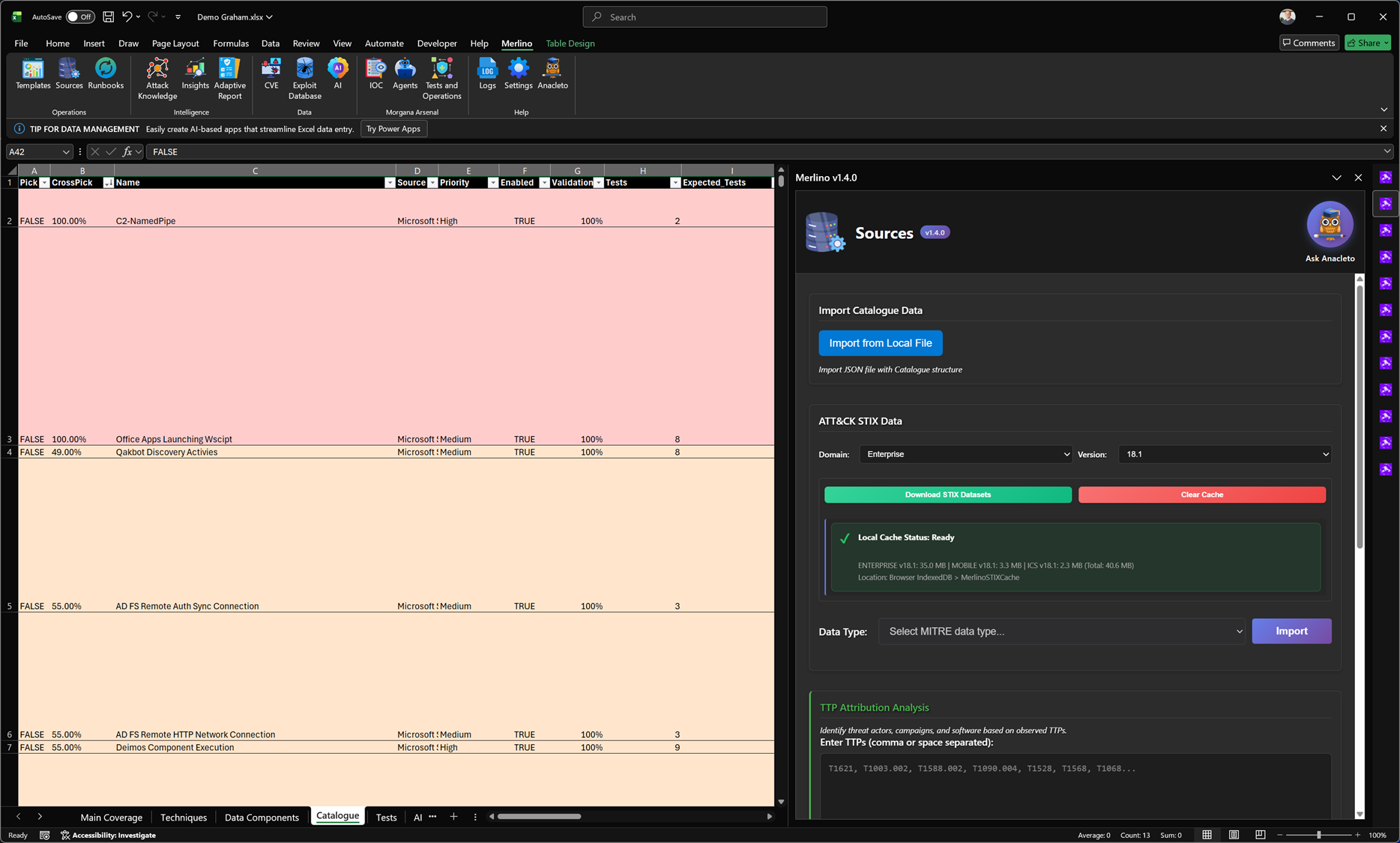
The Sources module is where Merlino builds the data foundation for all posture views, coverage analysis, and validation workflows. From here you can import authoritative datasets from MITRE ATT&CK and bring in structured catalogue data from security platforms (e.g., Microsoft Sentinel, Dynatrace, Intune, and other integrations). New sources are added periodically as Merlino evolves.
What this module does
-
Import MITRE ATT&CK datasets (STIX)
Download selected ATT&CK domains and versions, cache them locally for speed, and import the required data types into your workbook tables. -
Import catalogue data from security sources
Load structured data from supported security tools and platforms to create a unified reference catalogue used across Merlino analysis and test planning. -
Enable downstream analysis and testing
The imported datasets become the engine behind posture dashboards, technique coverage, detection alignment, prioritisation, and validation workflows.
ATT&CK STIX Data (Download & Import)
Select the domain and version, download the datasets, and import the data types you need. Merlino stores datasets locally (cache) to improve performance and ensure repeatability.
- Download STIX Datasets – retrieves the selected ATT&CK datasets for offline-ready usage.
- Local Cache Status – shows whether the dataset is available and ready.
- Clear Cache – removes cached datasets to refresh or reclaim space.
- Import – imports the chosen ATT&CK data type into the workbook tables.
Import Catalogue Data
Use Import from Local File to load a Merlino-compatible JSON catalogue into your workbook. This is typically used to import source capabilities, mappings, and curated datasets that power analysis and validation.
TTP Attribution Analysis (Heuristic Intelligence Suggestions)
Merlino can perform dynamic TTP-driven enrichment. Provide a list of observed ATT&CK technique IDs and Merlino applies heuristic analysis to suggest the most likely CTI context from MITRE knowledge bases, such as:
- threat actor / hacker group candidates
- campaign hypotheses
- related software and tooling patterns
- additional context to accelerate investigation and prioritisation
This helps analysts move faster from “what we observed” to “who it resembles” and “what we should validate next”, without manually searching across multiple sources.
Notes
- New sources and catalogues are introduced periodically as Merlino expands.
- Imported data becomes the shared reference layer used across analysis, validation, and reporting.
